The past five days have been riveting following the invasion of Ukraine. Upon witnessing mass destruction by Russian military forces, nations across the globe respond. Vulnerable populations are taking refuge during the war. Both countries suffered military and civilian casualties from explosions and attacks. Meanwhile, hundreds of thousands have joined Ukraine’s “IT Army”. Underground hackers are fighting in the cyberwar against Russia’s advanced cyber adversaries. CyberKnow is an organization that provides situational awareness reports, OSINT investigations, and discusses geopolitical situations that impact cyberspace. They have published an updated list of cyber groups involved in the Ukrainian-Russian War.
Anticipating Russian Cyber Operations
A few weeks ago, Mandiant analysts shared a timely cyber talk, “Anticipating Russian Cyber Operations”. They released a 40-page guide, “Proactive Preparation and Hardening to Protect Against Destructive Attacks”. Available at: https://www.mandiant.com/resources/protect-against-destructive-attacks. Within Mandiant’s Assessed Structure of Russian Cyber Programs, Mandiant identified three threat actors focused on cyberattack: Sandworm Team, TEMP.Isotope, TEMP.Veles.
Sandworm Team’s destructive attacks have had a devastating impact throughout cyber history. Associated groups who operate within Russian state interests include Voodoo Bear, BlackEnergy APT Group, Telebots, Iron Viking, Quedagh, and Electrum. MITRE ATT&CK has documented a few of their known attack techniques and software used: https://attack.mitre.org/groups/G0034/.
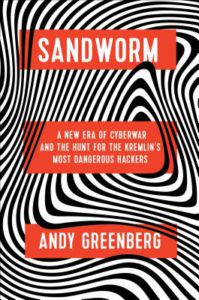 Andy Greenberg is a senior writer for Wired Magazine who covers security, privacy, information freedom, and hacker culture. He gave a chilling narrative account of his investigation into Sandworm hackers’ exploits in his book, “Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin’s Most Dangerous Hackers“. Tech Crunch shared, “A beautifully written deep-dive into a group of Russian hackers blamed for the most disruptive cyberattack in history, NotPetya, This incredibly detailed investigative book leaves no stone unturned, unraveling the work of a highly secretive group that caused billions of dollars of damage.”
Andy Greenberg is a senior writer for Wired Magazine who covers security, privacy, information freedom, and hacker culture. He gave a chilling narrative account of his investigation into Sandworm hackers’ exploits in his book, “Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin’s Most Dangerous Hackers“. Tech Crunch shared, “A beautifully written deep-dive into a group of Russian hackers blamed for the most disruptive cyberattack in history, NotPetya, This incredibly detailed investigative book leaves no stone unturned, unraveling the work of a highly secretive group that caused billions of dollars of damage.”
A Brief History of Sandworm’s Attacks
-
2015 – BlackEnergy’s disrupted Ukraine’s electricity by triggering blackouts. 230,000 people lost power between 1 to 6 hours.
-
2016 – Industroyer’s malware framework is a big threat to industrial control systems. Industroyer shut off Ukraine’s electricity grid known as Crash Override. One-fifth of Kyiv’s population lost power for an hour.
-
2017 – NotPetya’s crippling malware targeted Ukraine’s financial, energy, and government sectors. Other European and Russian businesses were also affected. It has spread globally resulting in over $10 billion in damage.
-
2018 – Olympic Destroyer’s malware disabled the network at the Winter Olympics and Paralympics. Cisco Talos Intelligence blog gives a solid overview of the Destroyer’s workflow.
-
2019 – Disruptive attacks against Georgia include website defacement and interrupted TV channels
Pyeongchang Winter Olympics 2018 was hit by a cyberattack during the opening ceremony in Korea
Cautionary Tales for San Antonio’s Cybersecurity Ecosystem
“The whole objective of Russia is to smother the West and put all of us in the dark ages. The cyber war is real, and we’re facing it in Ukraine. You can all learn from what’s happening in Ukraine.”
– Dmytro Shymki